E-Crime
E-Crime
A Guide to E-Crime Investigations
© New Zealand Police 2002
Produced by the Research and Development Group,
Training Service Centre.
This information is for Police use only.
Appendix A
Contents
Wording to be included in a search warrant
Preface ............................................................. 1
Computers, central processing units, external and internal
Introduction ..................................................... 2
drives and external storage equipment or media, terminals or
video display units, together with peripheral equipment such
Part I The Internet and How it Works
as keyboards, printers, scanners and modems.
Equipment to connect online ................................................... 3
The Internet .............................................................................. 4
World wide web ........................................................................ 5
Any and all computer or data processing software or data
Usenet and newsgroups .......................................................... 6
including, but not limited to, hard disks, floppy discs, cassette
Internet relay chat (IRC) ........................................................... 7
tapes, video cassette tapes, magnetic tapes, integral RAM or
Electronic mail .......................................................................... 8
ROM units and any other permanent or transient storage
Key points ................................................................................ 9
device(s).
Part II Case Examples .................................. 10
The following records or documents, whether contained on
Part III Electronic Evidence
paper in handwritten, typed, photocopied or printed form or
Sources of evidence .............................................................. 13
stored on computer print-outs, magnetic tape, cassettes,
Key points .............................................................................. 15
discs, diskettes, photo optical devices or any other medium:
Examples of Electronic Devices ............................................. 16
access number(s), password(s), pass-phrase(s), personal
Part IV Best Practice
identification numbers (PINS).
First response ........................................................................ 18
Device types .......................................................................... 20
Any computing or data processing literature, including, but not
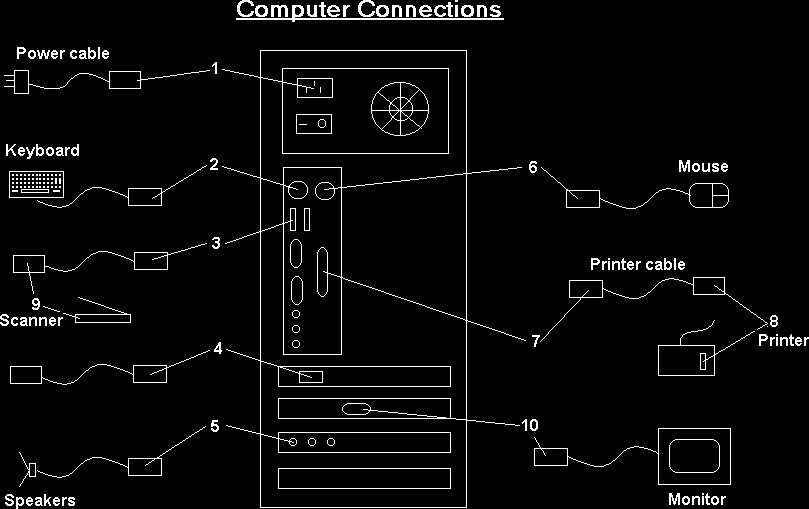
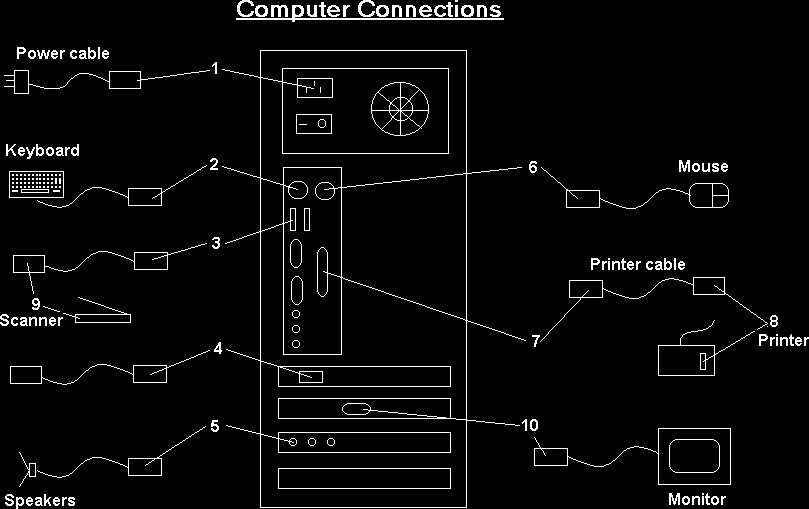
Computer Diagramming ........................................................ 23
limited to, printed copy, instruction books, notes, papers or
Non-electronic evidence ........................................................ 25
listed computer programs in whole or in part.
Care and submission of exhibits ............................................ 26
Key points .............................................................................. 27
Conclusion ..................................................... 28
Glossary ......................................................... 29
Appendix
Wording to be included in a search warrant .......................... 35
© NZ Police
35
Preface
Virus attacks and worms: A program or piece of code that is loaded
onto your computer without your knowledge and runs against your
wishes. Viruses can also replicate themselves. Even a simple
This booklet supports the accompanying video and is
replicating virus is dangerous because it will quickly use all available
designed to raise your awareness and understanding of
memory and bring the system to a halt.
electronic crime. The booklet will not make you an expert but
Some people distinguish between general viruses and worms.
it will provide you with some ideas on how to identify and deal
A worm is a special type of virus that can replicate itself and use
with electronic crime (e-crime).
memory, but cannot attach itself to other programs.
Note: If you come across any devices in the field that you
Endnotes
are not familiar with or if you have any doubts about dealing
1 http://www.techweb.com/encyclopedia/
2
with such devices, contact your nearest Electronic Crime
Law Commission Computer Misuse, Report No 54, 1999, 54.
3 http://www.pcc.philips.com/glossary/p-z.shtml
Laboratory (ECL) at Auckland, Wellington or Dunedin.
4 http://www.techweb.com/encyclopedia/
Your local Comms Centre has an after-hours contact list.
Additional copies of the video and booklet can be obtained
from the Research and Development Group, Training Service
Centre.
© NZ Police
1
© NZ Police
34
PIN: Personal Identification Number.
Introduction
Posting: An article or message posted to a newsgroup.
Continuing advances in electronic technology and the growth
of the Internet have seen computers and other electronic
PUK code (PIN Unlocking Key): If PIN code has been entered
wrong three times, the SIM card cannot be used before the correct
devices become commonplace both in commerce and in the
unblocking PUK code has been given. If the PUK code is given
home, with New Zealanders having one of the highest per
wrongly 10 times the SIM card will be irrevocably locked.3
capita rates of computer ownership and Internet access in the
world.
SIM card (Subscriber Identity Module): A smart card inserted into
mobile phones that contains telephone account information.4
Criminals have not been slow to adopt this technology for their
own ends, both as a means to assist with the commission of
Smart card: A small electronic device about the size of a credit card
traditional offences and to instigate a range of new offences.
that contains electronic memory, and possibly an embedded
integrated circuit (IC). Smart cards are used for a variety of
Accordingly, electronic evidence is now seen across the full
purposes, including:
spectrum of offending and you need to be able to deal with
this evidence no matter what offence you are investigating.
*
storing a patient’s medical records
*
storing digital cash
*
generating network IDs (similar to a token).
With e-crime you have new questions to ask, new clues to
look for, and new rules to observe in the collection and
Software: Computer instructions or data. Anything that can be
preservation of evidence.
stored electronically is software. The storage devices and display
devices are hardware.
This booklet is divided into four sections:
*
Part I covers the Internet, what it is and how it works.
Spam: Electronic junk mail or junk newsgroup postings. Real spam
is generally e-mail advertising for some product sent to a mailing list
*
Part II gives examples of investigations where
or newsgroup.
electronic evidence helped gain convictions.
*
Part III investigates electronic evidence, for example
Usenet (also called netnews): A worldwide bulletin board system
computer components, storage devices, disks, tapes
accessed through the Internet. Items posted to the system are
and drives.
tagged with topics and become known as ‘newsgroups’. A news-
*
Part IV looks at “best practice” in regards to the
reading program (newsreader) is needed to read or post articles to
search, seizure and storage of electronic evidence.
a newsgroup. Articles can also be archived or downloaded.
A glossary of terms is provided at the back of the booklet
along with the wording to be used in a search warrant.
© NZ Police
33
© NZ Police
2
 Part I
ISP (Internet Service Provider):
Part I
ISP (Internet Service Provider): A company that provides access to
the Internet for a monthly fee. It provides the customer with a
The Internet and
software package, username, password and access phone number.
How it Works
Logic bomb: A nasty selection of codes that is covertly inserted into
a program or operating system. It triggers some activity whenever a
Equipment to connect online
specific condition is met. The activity is generally destructive.2
The online universe is made up of millions of interconnected
Modem: A modem is a device or program that enables a computer
computers. A computer connected to the Internet can
to transmit data over telephone lines. Computer information is stored
transport you via your computer to just about anywhere.
digitally, whereas information transmitted over telephone lines is
transmitted in the form of analog waves. A modem converts between
To connect to the Internet (or go online) you need a
these two forms.
computer, or other device, hooked to the Internet via a
telephone line, cable or satellite connection. A group of
Network: A group of two or more computer systems linked together.
networked computers can also share an Internet connection.
There are many types of computer networks, including:
*
local-area networks (LANs): The computers are
To access the Internet, specific “browser” software is needed
geographically close together (that is, in the same
to locate and display web pages, for example Microsoft’s
building).
*
wide-area networks (WANs): The computers are
“Internet Explorer”.
further apart and are connected by telephone lines or
radio waves.
To make the connection there also needs to be an account
*
campus-area networks (CANs): The computers are
with an Internet service provider (ISP), such as Paradise
within a limited geographic area, such as a university
(provided by Telstra Saturn) or Xtra (provided by Telecom).
campus or military base.
*
metropolitan-area networks (MANs): A data network
designed for a town or city.
When the browser software is activated, a password is
*
home-area networks (HANs): A network contained
entered for the ISP account. The modem dials up the ISP and
within a user’s home that connects a person’s digital
the user is assigned a unique identity, which is the Internet
devices.
Protocol (IP) address.
Newsgroup: Refer to
Usenet below.
By identifying the IP address you can trace back to the user
account at any given point in time. However, these records are
Palm pilot / PDA (Personal Digital Assistant): A handheld
kept by the ISP for only a short period.
computer. A typical palm pilot can function as a cellular phone, fax
sender, and personal organiser.
© NZ Police
3
© NZ Police
32
Flash Card: A small module that contains flash memory such as a
The Internet
PC Card, CompactFlash, SmartMedia or similar format.1
The Internet consists of the world wide web, Usenet newsgroups,
Internet relay chat, and electronic mail (e-mail).
Hacker: A slang term for a computer enthusiast – a person who
enjoys learning programming languages and computer systems and
Wherever someone goes on the Internet, what they do and
can often be considered an expert on the subject(s). The popular
press has coopted the term to refer to individuals who gain
who they correspond with or how, it is likely that their
unauthorised access to computer systems for the purpose of
computer will record some or all of those details. In many
stealing and corrupting data.
cases this process takes place without the user’s intervention
or knowledge and the resultant data ends up in areas on the
Hacking: Unauthorised access into computer systems.
hard drive to which the average user does not have easy
access.
Hardware: Refers to objects that you can actually touch, like disks,
disk drives, display screens, keyboards, printers, boards, and chips.
In contrast, software is untouchable.
Reconstructing this data will often give an accurate picture of
what has occurred. For this reason, if the circumstances
Internet Relay Chat (IRC): A chat system on the Internet that allows
warrant it, consider requesting the complainant to release
people to join live discussions online. To access IRC a special
their computer for forensic examination so that this material
program is needed that connects to an IRC server. An IRC user can
can be located and preserved.
access ‘chat rooms’ and communicate with other users via text
messages or web camera images.
Whenever someone joins or leaves a chat room a message is sent
to the rest of the participants. Users can communicate with all the
participants or send private messages to an individual. Users take
on a nickname while in a chat room and anything they type is
preceded by their nickname. The person behind the nickname can
register other information about themselves, such as e-mail address,
age and gender, that the other participants can access.
Intranet: A network belonging to an organisation accessible only by
the organisation’s members, employees, or others with authorisation.
An intranet’s web sites look and act just like any other web sites, but
the firewall surrounding an intranet fends off unauthorised access.
© NZ Police
31
© NZ Police
4
World wide web
*
hard disk: Hard disks can store anywhere from 20MB to
The world wide web consists of thousands of websites. The
more than 200GB. Hard disks are also from 10 to 100
times faster than floppy disks.
websites are generally either electronic shop fronts set up to
*
removable cartridge: Removable cartridges are hard
sell products and services or providers of information. Each
disks encased in a metal or plastic cartridge, so you can
website has a unique address known as uniform resource
remove them just like a floppy disk. Removable
locator (URL). The URL for the Police website is
cartridges are very fast, though usually not as fast as
www.police.govt.nz.
fixed hard disks.
While there are many legitimate sites, criminals take
Optical disks record data by burning microscopic holes in the surface
advantage of the medium to operate website scams.
of the disk with a laser. To read the disk, another laser beam shines
on the disk and detects the holes by changes in the reflection
Sometimes people try to find buyers for stolen goods on
pattern. Optical disks come in three basic forms:
legitimate websites. Criminals can set up websites to collect
credit card numbers and other personal information from
*
CD-ROM: Most optical disks are read-only. When you
purchase them, they are already filled with data. You can
customers who believe they are buying legitimate products or
read the data from a CD-ROM, but you cannot modify,
services. In reality nothing is ever delivered. The criminal then
delete, or write new data.
sells the stolen information or uses it for his or her own (illegal)
*
WORM: Stands for
write-
once,
read-
many. WORM disks
purposes. This is becoming known as identity fraud/theft.
can be written on once and then read any number of
times. You need a special WORM disk drive to write data
Questions to ask in a website investigation
onto a WORM disk.
*
erasable optical (EO
): EO disks can be read to, written
to, and erased just like magnetic disks.
1.
What is the address or uniform resource locator (URL)?
2.
How did the complainant become aware of the
DVD (Digital Versatile Disc or Digital Video Disc): A new type of
existence of the website?
CD-ROM that holds a minimum of 4.7GB (gigabytes), enough for a
3.
When did the complainant contact the website?
full-length movie.
4.
Did the complainant print a copy of the screen image? If
so, ask for a copy.
Encryption: The translation of data into a secret code. Encryption is
5.
Did the complainant save a copy of the website in his or
the most effective way to achieve data security. To read an encrypted
file, you must have access to a secret key or password that enables
her computer? If so, ask for a copy on floppy disk.
you to decrypt it. Unencrypted data is called plain text; encrypted data
6.
Obtain the username, logon and password used to
is referred to as cipher text.
access the website.
There are two main types of encryption: asymmetric encryption (also
7.
Consider requesting the complainant to release the
called public-key encryption) and symmetric encryption.
computer for forensic examination.
© NZ Police
5
© NZ Police
30
Glossary
Usenet and newsgroups
Another major aspect of the Internet is Usenet (also called
Note: These definitions have been adapted from the Webopedia
netnews), which is made up of newsgroups. Newsgroups are
website http://www.pcwebopedia.com, except where indicated. Visit
like notice boards or discussion forums and are usually
this site if you have any further questions regarding terms used in
subject specific. Messages can be read from or posted to a
this booklet.
newsgroup (a message posted to a newsgroup is called a
posting). Copies of messages can also be downloaded onto
Browser: Short for Web browser, a software application used to
a computer.
locate and display Web pages. The two most popular browsers are
Netscape Navigator and Microsoft Internet Explorer.
There are newsgroups that collect and distribute child
CD-ROM: A compact disc made out of a polycarbonate with one or
pornography and advertise children available for sex. Thieves
more metal layers capable of storing digital information. CD-ROMs
use newsgroups to advertise stolen goods for sale. Illicit drug
are used to store computer data. They are read-only, which means
manufacturers discuss production techniques and may
that once the data has been recorded onto them, they can only be
purchase equipment online through these groups. For more
read or played.
information on Usenet and newsgroups, see the Glossary.
Chat room: A virtual room where a chat session takes place.
Technically, a chat room is really a channel, but the term “room” is
Questions to ask in a newsgroup investigation
used to promote the chat metaphor.
1.
Who is the complainant’s Internet service provider (ISP)?
Chat session: A way of communicating in real time via a computer.
2.
How did the complainant discover the existence of the
Two or more parties type messages to each other, which are
newsgroup?
received immediately.
3.
What is the name of the newsgroup?
4.
What is the name of the posting?
Disk: A round plate on which data can be encoded. There are two
basic types of disks: magnetic disks and optical disks.
5.
Does the complainant have a printed copy of the
posting? If so, ask for a copy.
On magnetic disks, data is encoded as microscopic magnetized
6.
Did the complainant download the posting onto their
needles on the disk’s surface. You can record and erase data on a
computer? If so, ask for a copy on floppy disk.
magnetic disk any number of times, just as you can with a cassette
7.
Obtain the username, logon and password used to
tape. Magnetic disks come in a number of different forms:
access the newsgroup.
*
floppy disk: A typical 5¼-inch floppy disk can hold
8.
Consider requesting the complainant to release the
360K or 1.2MB (megabytes). 3½-inch floppies normally
computer for forensic examination.
store 720K, 1.2MB or 1.44MB of data.
© NZ Police
29
© NZ Police
6
Internet relay chat (IRC)
Conclusion
Internet relay chat is another major aspect of the Internet.
It consists of thousands of “chat rooms” where people
More criminals now commit their crimes electronically,
communicate in near “real time” using text messages.
including online via the Internet. It is quick, easy and assumed
anonymous. However, the police know more than these
Paedophiles meet in chat rooms to discuss their sexual
criminals think.
exploits. Paedophiles and other sexual predators visit chat
rooms catering for children and teenagers. They often pose as
By taking care to follow best practice, valuable evidence is
teenagers to lure young people into sexual relationships in the
more likely to be found. This booklet and accompanying video
real world (off-line).
do not provide all the answers, but you will now have enough
Fraudsters work in chat rooms developing relationships and
basic knowledge to deal with the situation and know when to
looking for people who will fall for their phoney business
call the ECL for their expert advice.
opportunities and get rich schemes. For more information on
Internet relay chat, see the Glossary.
Questions to ask in a chat room investigation
1.
What is the name of the chat room or chat channel?
2.
What is the name of the server the chat room is on?
3.
What is the nickname, “handle” or screen name of the
offender?
4.
Did the complainant note the person’s Internet Protocol
(IP) address next to their screen name in the users list?
If so, ask for the IP address.
5.
Did the complainant print a copy of the chat dialogue
window? If so, ask for a copy.
6.
Obtain the username, logon and password used to
access the website.
7.
Did the complainant save the chat dialogue on their
computer? If so, ask for a copy on floppy disk.
8.
Consider requesting the complainant to release the
computer for forensic examination.
© NZ Police
7
© NZ Police
28
Key points
Electronic mail
Electronic mail (e-mail) is the transmission of messages or
• Keep the suspect away from the computer or device.
files over a communication network. Many organisations have
• If the computer or device is ON, do not turn it off.
an internal e-mail system (intranet) as well as access to the
• If it is OFF, do not turn it on.
Internet and the ability to send e-mail messages world wide.
• For stand-alone computers, photograph or sketch a
picture of the back of the computer. Number connections
Criminals sometimes market their fraudulent scams through
and cables.
e-mail. This unsolicited, “junk” e-mail is called spam (although
• For business or networked computers, contact ECL for
not all spam is illegal).
advice.
• Before submitting electronic items for fingerprinting or
E-mail messages carry a source header that records the
other forensic testing, contact ECL.
IP address of the original source and any subsequent
transmissions of the e-mail. Usually, this information is not
visible when the user views the e-mail.
Questions to ask in an e-mail investigation
1.
What is the name of the Internet service provider (ISP)?
2.
Does the complainant have a printed copy of the e-mail
message (ideally including the complete header)? If so,
ask for a copy.
3.
Did the complainant save a copy of the e-mail message
on their computer? If so, ask for a copy on floppy disk.
4.
If the complainant does not have a copy of the e-mail
message, is it still in the “computer mailbox” at the ISP?
If so, ask for a copy on floppy disk.
5.
What is the offender’s screen name and e-mail address?
6.
What is the complainant’s username, logon and
password.
7.
What e-mail program was the complainant using?
8.
Consider requesting the complainant to release the
computer for forensic examination.
© NZ Police
27
© NZ Police
8
What attracts a lot of criminals to the Internet is the ability to
Care and submission of exhibits
remain anonymous. However, the irony is that it is almost
impossible not to leave some sort of electronic trail.
Ensure that as far as is practicable none of the actions taken
add, modify or destroy data stored on a computer, device or
Key points
media.
•
Computers record data from Internet use. This data can
Remember computers and related electronic equipment are
be located and preserved as evidence.
fragile and sensitive to shock, temperature and moisture.
•
Tailor your questions to the type of Internet use
suspected.
Items submitted to the ECL should be appropriately packaged
and cushioned with bubble wrap and/or polystyrene. The
external packaging should be clearly marked as fragile.
When submitting material to the ECL include the following
items and information as appropriate:
-
brief circumstances of the case
-
the known history of the items submitted
-
specific details of the examination required
including any keywords to be searched against
-
specific details of the items being submitted
-
a copy of the warrant items were seized under
-
a copy of the POL 268 form
-
contact details of the submitter
-
details of any other forensic testing proposed.
Contact the ECL before submitting electronic items for
fingerprinting or other forensic testing if there is likely to be
a requirement for these items to be examined by the ECL at
some later date. This is because some of the treatments
used by other forensic disciplines can damage or destroy
electronic items.
© NZ Police
9
© NZ Police
26
In summary:
Part II
1.
Sketch the rear of the computer.
E-Crime Examples
2.
Number each socket or port that has a cable connected
to it and note this number on your sketch.
3.
Attach the corresponding number to the end of the
cable that is attached to the computer.
These case examples show that time spent finding and
4.
If the computer has cables attached to its front, sketch
preserving electronic evidence can pay huge dividends to the
and label those as well.
outcome of the investigation.
If you have any doubts or concerns, contact the ECL.
Operation Ono
This operation took place in Auckland City from August to
Non-electronic evidence
December 1999. The electronic evidence found included an
electronic diary and Vodafone cellphones. From that evidence
Recovery of non-electronic evidence can be crucial in the
Police extracted dates and times of drug sales and names of
investigation of electronic crime. Proper care should be taken
customers. As a result of the evidence five people were
to ensure that such evidence is recovered and preserved.
convicted for manufacturing methamphetamine, conspiracy to
manufacture methamphetamine, and selling Class A, B and C
Items relevant to subsequent examination of electronic
drugs. The prison sentences ranged from 5 to 12 years.
evidence may exist in other forms, for example written
passwords and other handwritten notes, blank pads of paper
Teenage Hacker Case
with indented writing, hardware and software manuals,
Staff from Paradise (an ISP) were contacted by a customer
calendars, literature, text or graphical computer printouts, and
who had been unable to log on to the Internet. They
photographs.
established that someone else was using the customer’s
account and identified the originating phone number that had
These items should be secured and preserved for future
fraudulently accessed her account details. Paradise agreed
analysis. These items are often located near the computer or
to contact the investigators next time the offender was online.
related hardware items. All evidence should be identified,
When the investigators were advised, they were ready to
secured, and preserved in compliance with General
execute a search warrant within a couple of minutes. They
Instructions and district policy.
found a 17-year-old hacker with the account holder’s details
on screen. Relevant computer items were seized.
© NZ Police
25
© NZ Police
10
The investigators discovered that the offender had distributed
If the other end of the cable can be unplugged from an
passwords to his friends and he and those friends were
external unit (eg printer, monitor, scanner), unplug it, give that
illegally accessing other accounts.
end of the cable its own number and, if possible, show on
your diagram what the cable was attached to.
The offender was charged with “using a document” and was
ordered to pay reparation, send letters of apology and do 80
By using numbers it doesn’t matter if you are unsure what type
hours’ community service. The friends were not charged due
of socket or port a particular cable connects to. If you can
to their age, but were referred to Youth Aid.
identify the external units the cable connects to, such as
mouse, keyboard and printer, those details will be helpful.
Operation Godlee
This was a high-profile homicide investigation running from
An example of this type of sketch is shown below.
August to September 2000. Three members of a gang
committed a homicide in the Christchurch Port Hills at Godley
Heads.
In an attempt to become affiliated to an overseas gang, the
leader of the Christchurch gang had surfed the web and e-
mailed two gangs. A Canadian gang e-mailed back, asking
for proof of how ‘bad’ he was before he could be accepted.
As a result the leader decided to kill one of the other gang
members. He and two others took the victim to Godley Heads,
carried out the murder, then sent a text message saying
“Done”. The day after the murder, the leader e-mailed the
Canadian gang and asked them whether they could get a
copy of the Christchurch Press as the murder he had
organised would be in it. This e-mail pre-dated any press
releases or articles relating to the homicide.
The investigators were able to find electronic evidence in the
form of e-mails, text messages and messages sent through
chat rooms. All three men were found guilty of murder.
© NZ Police
11
© NZ Police
24
If you are out of town, make an assessment as to the
Hawkins Case
seriousness of the offence and the kind of information likely to
An 8-year-old girl sparked a paedophile investigation when
be on the phone. Obviously, if a cell phone is found at a
she complained of being indecently touched and violated. In
homicide scene then it should be transferred to the nearest
the evidential interview the victim told of how she was shown
ECL as soon as possible.
photos of naked people on a computer. The investigators
seized the offender’s computer, computer-related items and a
Collect all contract documentation with the warrant, for example
digital camera.
PUK codes, and any other documentation related to the cell
phone.
The hard drive revealed thousands of pictures downloaded
from the Internet and 54 pictures of a second victim that had
Other devices
been taken with the digital camera, downloaded to the hard
Apply the same basic rules as for cell phones. If it is off leave
drive then saved on a floppy disk.
it off, if it is on leave it on. Be aware that battery powered
devices will die when the battery is exhausted, which may
The offender was convicted with three charges of rape
activate a lockout or data loss.
and 22 charges of sexual offending. He was sentenced to
11 years’ jail.
Computer Diagramming
When you submit a seized computer to the ECL, you must
have ensured the ECL experts can reassemble the computer
exactly as it was found. It is essential the ECL knows where
the various cables were attached. One reason for this is that
many systems have multiple sockets or ports that are for the
same purpose. For example there may be two monitor ports,
or two sets of audio connections. The ECL needs to know
which sockets or ports were in use on an individual system.
An easy method to document the cabling is to sketch the rear
of the computer and on the diagram number each socket that
has a plug in it. Physically attach the same number to the end
of the cable that is plugged into the computer. This number
can be attached with a sticker or by tying a label to the cable.
© NZ Police
23
© NZ Police
12
If a suspect or any other person is in attendance at the scene,
Part III
question them to obtain information, such as the owners and/
Electronic Evidence
or users of the electronic devices found at the scene,
passwords, usernames, encryption codes and ISP.
Other electronic devices can contain valuable evidence
In the New Zealand Police there are specialist forensic
associated with criminal activity. Unless an emergency exists,
examiners and analysts at the Electronic Crime Laboratory
the device should not be accessed. Should it be necessary to
(ECL) in Auckland, Wellington and Dunedin who carry out the
access the device, all actions associated with the
examination of devices.
manipulation of the device should be noted to document the
chain of custody and ensure its admission in court.
Electronic evidence can be latent in the same sense that
fingerprint or DNA evidence is latent. Latent evidence is
Cell phones
evidence that is not easy to “see”, so specialist equipment
If the cell phone:
and/or software is needed to make the evidence visible.
➨
is off, leave it off
Files can be created, such as documents, e-mail messages,
➨
is on, leave it on
database information, photo files and video files. However,
➨
is on, photograph the display or write down the
the computer also creates files that document the use of the
information on the screen
device, such as date and time stamps, history files of
➨
is on and you are near the ECL, take the phone
websites visited, and temporary files for unsaved documents.
straight to the ECL
Some electronic evidence is time sensitive and as such this
➨
is on and you are far from the ECL, attach the
class of evidence should be dealt with promptly.
phone to a battery recharger
Recognising the potential evidence that may exist on an
➨
rings, do not answer it.
electronic device could be vital to the successful resolution
of the crime.
If the cell phone is on, be aware that turning it off or letting the
battery run flat may activate a security lock-out device that will
Sources of evidence
make it almost impossible for the ECL to turn the phone on
All computers, whether a stand-alone PC or a laptop, contain
again.
one or more hard drives. A huge amount of data can be
stored on the hard drive. It is a prime source of evidence.
The hard drive can be taken out of the computer and hidden
elsewhere.
© NZ Police
13
© NZ Police
22
3.
Using sticky labels or similar, label the components and
Data can also be stored on various other removable storage
existing connections at the back of the computer. Label
devices, including disks, drives and tapes. These can be
all connectors and cables at each end. This will enable
small and are portable, making them easy to hide or disguise.
reassembly if needed.
A CD-Rom containing evidence can be disguised as a music
CD.
4.
Photograph the back of the computer or sketch a
diagram. For information on computer diagramming
The amounts of data on modern devices can be huge. When
see page 26.
you require ECL staff to examine a device you must give them
specific details of what you are looking for. The more detailed
5.
Place tape over each drive slot.
your information, the more efficient the search.
6.
Collect all removable storage media and documentation.
Note: To give you an idea of the size of the search task, if the
contents of a full 40GB hard drive were printed out as text it
7.
Obtain all logons, usernames, passwords and PIN
would produce a stack of A4 pages 1,500 metres high. This is
numbers.
over 4½ times the height of the Auckland Sky Tower. Even a
3½” floppy disk can carry enough information to print in
Note: It is common for people to write their passwords down
excess of a ream of paper. Therefore, it is important to be as
and leave them on or near the computer. Keep an eye out.
detailed as possible in your search request to an ECL.
Networked or business computers
Remember: A computer and its related storage devices are
If the computer is networked or a business computer consult
not the only electronic devices from which evidence can be
the ECL for further assistance. If possible, call the ECL before
collected. Most electronic devices contain some kind of
you execute the warrant. Pulling the plug could severely
memory function that may be accessible and hold useful
damage the system and disrupt legitimate business leaving
information. Ask for logons, usernames and passwords
ds for
the Police open to official complaint and the possibility of civil
these devices as appropriate.
action.
Electronic devices that exist today include:
Remember: Keyboards, the computer mouse, disks, CDs,
and other components may have fingerprints or other physical
Cellular and mobile telephones
evidence on them that should be preserved in the usual
SIM cards
manner.
Digital cameras and videos
© NZ Police
21
© NZ Police
14
Scanners
Device types
Palm pilots or PDAs
Facsimile (fax) machines
Stand-alone, non-networked computer
Electronic diaries and organisers
Note: If the screen is blank do not automatically assume that
Pagers
the computer is off, it may have gone into “hibernation” mode.
Flash cards
You should determine whether the computer is actually on or
Smart cards
off by moving the mouse – if the computer is on the screen
Photocopy machines
should reactivate.
Removable media storage devices (there is a multitude of
different types)
DO NOT TOUCH THE KEYBOARD OR MOUSE BUTTONS.
These devices come in a range of shapes and sizes and can
If computer is off, DO NOT TURN IT ON.
be easily disguised.
If computer is on
on, DON’T TURN IT OFF.
Key points
If there is material on the screen about which you are unsure,
• Many electronic devices have memory devices that can hold
call the ECL before you take any further action.
useful information.
• Electronic evidence can be time sensitive – you must deal
Then
with it promptly.
1.
Consider photographing the screen if the material on the
• The hard drive is a prime source of evidence.
screen is relevant.
• The recovery of electronic evidence requires specialised
knowledge and technology.
2.
Pull out the power plug from the back of the computer
• Give ECL staff specific details of what you are looking for.
first and then from the wall. If the computer is a laptop
you will also have to remove the battery, look for a large
latched panel usually marked with a battery icon. Do not
replace the battery once you have removed it.
This will instantly stop the computer if it is on and
remove the possibility of someone restarting it.
© NZ Police
15
© NZ Police
20







1.
Freeze the scene
Examples of Electronic Devices
Freeze the scene for potential fingerprints and other forms of
forensic evidence. Immediately restrict access to the
computer and other electronic devices and related material
(for example floppy disks). Do not attempt to access
information on the computer at this stage.
Digital Cameras
Do not allow the suspect near the computer or device as
electronic data can be altered or destroyed within seconds.
Criminals write “logic bombs” that can cause a computer to
crash and destroy data if the correct sequence of keystrokes
is not used.
2.
Locate and secure the evidence
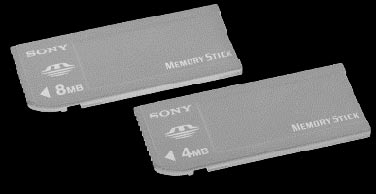
Memory Stick
Isolate the computer from telephone lines, as data on the
Reader Mouse
Flash Card Reader
computer can be accessed remotely. Identify telephone lines
attached to devices such as modems and caller identification
(ID) boxes. As the computer end of a telephone cable
appears very similar to a network cable it is better to
disconnect telephone lines from the wall rather than the
device where possible.
Secure the computer as evidence.
Electronic Organisers
Turning a computer on or off can alter the components of
evidential files, such as date and time stamps and
modification, deletion or user name attributes. In effect, this
alters the evidence and affects its admissibility in court.
Flash Card
Smart Card
Memory Sticks
© NZ Police
19
© NZ Police
16




 Part IV
Part IV
Best Practice
Electronic evidence is delicate. It is easily altered, damaged
Facsimile
Photocopier
or destroyed by improper handling or examination. It is
important to know when to call in experts from the ECL.
Any attempt to access data or run a computer program can
jeopardise the integrity of the evidence. Electronic evidence,
like all other evidence, must be handled carefully and in a
manner that protects its evidential integrity.
Pager
Note: If you are planning to execute a warrant and have
Scanner
concerns about what you may find or how to handle electronic
equipment call the ECL before you execute the warrant.
Wording to include in the warrant is outlined at the end of this
booklet.
First response
Freeze – locate – secure – document – protect
ZIP Drive
As a first responder, it is necessary to:
1. freeze the scene
2. locate and secure
e the evidence
3. document any action taken to ensure the evidential trail
4. protect perishable data physically and electronically.
Cellphone
© NZ Police
17
© NZ Police
18